Data is everywhere in the modern business world, and we rely on it every hour of the working day for the smooth running of our business operations. Businesses cannot function without data, and such a priceless commodity needs to be protected accordingly. Throughout its lifespan, great care is taken to protect the security and integrity of business data, and far reaching legislation such as the GDPR standardising the management of personal information, and imposing crippling fines on companies who do not take data protection seriously.
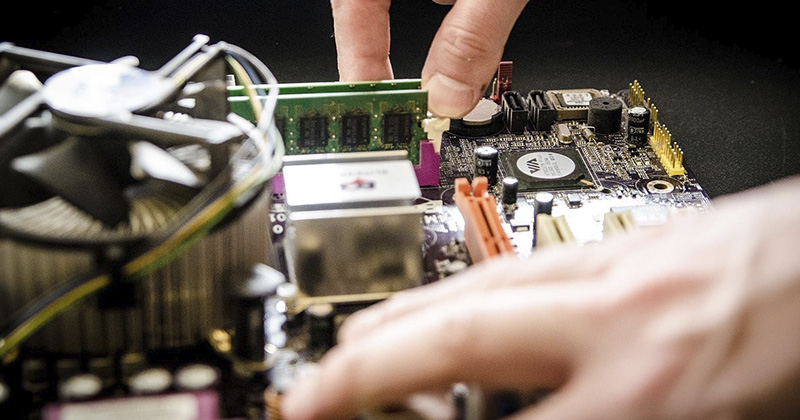
One of the most important aspects of data security is the management of data which reaches the end of its lifespan. Devices such as hard drives, mobile devices, laptops and servers will all become outdated and pass into disuse at one point or another, and how this process is handled is just as important as the secure management of data bearing devices that remain in use.
One of the most popular methods of securing data on end of life IT assets is data destruction. In this article we ask ‘what is data destruction’, and examine the three main data destruction methods: Overwriting, Degaussing, and Physical Destruction.
What is Data Destruction?
Data destruction is the process of destroying data contained on information bearing devices. Following the destruction process, the data is rendered irretrievable by anyone who later comes into possession of the technology.
In this sense, data destruction is distinct from the deletion of files. A file deleted on a business device such as a laptop may be inaccessible to the end user, but the information remains in some form on the device’s hard drive. Data destruction is the process of destroying this data in its entirety, making it impossible to be recovered.
Data destruction can be undertaken in a number of ways, but in this article, we will examine the three main methods:
- Overwriting – The process of covering up old files with new files
- Degaussing – The erasure of the magnetic field contained in storage media
- Physical Destruction – The physical destruction of data bearing devices through methods such as disk shredding
Overwriting
One of the most common forms of data destruction, overwriting erases data by overwriting it with new files. The process is undertaken using specialist software which writes a pattern of zeroes and ones over the existing information, rendering the data previously contained the device unreadable. In many cases, data will only need to be overwritten once to destroy the data, but for highly sensitive data bearing devices multiple wipes may be required to ensure complete security. There are many pieces of software which can be used for the purpose of overwriting, but not all comply with National Cyber Security Centre’s (NCSC) standards for the secure sanitisation of storage media. Software which does not comply with these standards should not be used in the disposal of business IT assets, and you should ask your IT asset disposal whether the software they use meets these standards.
While overwriting is effective for many cases of data destruction, it does have its limitations. The process can be lengthy; to overwrite a high capacity drive, for instance, can take a long time depending on the software used. It is also ineffective in instances where the hard drive is damaged or unreadable, which may be the case for assets which have been upgraded due to wear and tear. The relative ease of use of overwriting also presents its own problems, as, entrusted to the wrong hands, errors can occur where data remains accessible even after the data erasure process. On the flipside, overwriting is a cost effective and sustainable to approach to data destruction, as the hard drive is preserved and can subsequently be reused again.
Degaussing
The process known as degaussing is a form of data destruction which works by disrupting the magnetic field contained in the storage disk or drive. This process is carried out using a high-powered magnet known as a degausser. When the degausser is applied to a magnetic storage device the storage media contained within is quickly and effectively purged of its data. Following the degaussing process, the data is completely irretrievable.
While degaussing offers a secure approach to data security, there are some downsides to consider. For example, degaussing equipment can be heavy and cumbersome, as well as pricey. The strength of the degaussing magnet also means that the hard disk is generally destroyed entirely, as the disruption of the magnetic field essentially destroys the mechanisms of the hard-drive. Degaussing is also a specialised process, and should only be entrusted to fully-qualified IT asset disposal vendors.
Physical Destruction
Arguably the most effective method of data destruction is that of physical destruction. There are many different approaches to the physical destruction of data, such as incineration, shredding or pulverising, but the end result is the same – the complete destruction of any data bearing disk or drive.
The attraction of physical destruction is the guarantee of data security it ensures. A hard drive that has been destroyed physically is impossible to be reconstructed, rendering the information contained within completely unrecoverable. A coarse method of physical destruction is to drill directly through a hard drive, but IT asset disposal specialists utilise specialist equipment to shred or pulverise hard drives.
Physical destruction is also not without its drawbacks. Physical destruction is costly and generally inefficient, as the device is rendered worthless, preventing any opportunities for remarketing.
There are many factors to consider when it comes to data destruction, and we would always recommend partnering with an experienced IT asset disposal vendor rather than undertaking the process yourself. The different methods outlined in this article each have their own unique benefits and drawbacks, and it is often the case that a method that works well for one device, such as a laptop, would not be suitable for something such as a server. Another factor to consider is whether your IT assets will undergo data destruction onsite or offsite. Onsite data destruction can be undertaken using mobile degaussing or physical destruction equipment, as well as with erasure software, however, this will often entail hiring a specialist to visit your site to carry out the destruction. On the other hand, if your assets are transported offsite to undergo data destruction then you will need to ensure that each piece of equipment is tracked and accounted for throughout its journey, a process known as the chain-of-custody. If your IT assets are due to be shipped offsite for destruction then you should insist that your vendor is able to provide you with a fully auditable chain-of-custody to ensure you are protected legally in the event of a data breach.
With over 25 years industry experience, tier1 are proud to be the UK’s most accredited ITAD supplier. We possess the skills, accreditations and experience to handle our clients’ data with the care they deserve, and to dispose of it responsibly and legally.
We provide data destruction services to standards set by the NCSC, with certificated proof of erasure and destruction for every hard drive or data bearing asset. We ensure that your business remains compliant with GDPR/Data Protection Act when disposing of your retired IT Assets. Our IT Shredding service allows for the complete destruction of data, whether it is the shredding of hard drives or any other form of media bearing items. Contact us today on 0161 777 1000 or visit https://www.tier1.com to discuss our industry-leading data destruction services.