EOL IT Services has now merged with tier1 Asset Management Ltd
People. Planet. Profit
Let’s work together to shape a future that works for all.
Sustainability is no longer an option, it is an essential element of every corporate strategy. Here at tier1 our ethos of ‘Reduce. Reuse. Recycle’ remains central to all that we do.
Our mission is to drive decarbonisation through our sustainable and socially responsible, circular economy business.
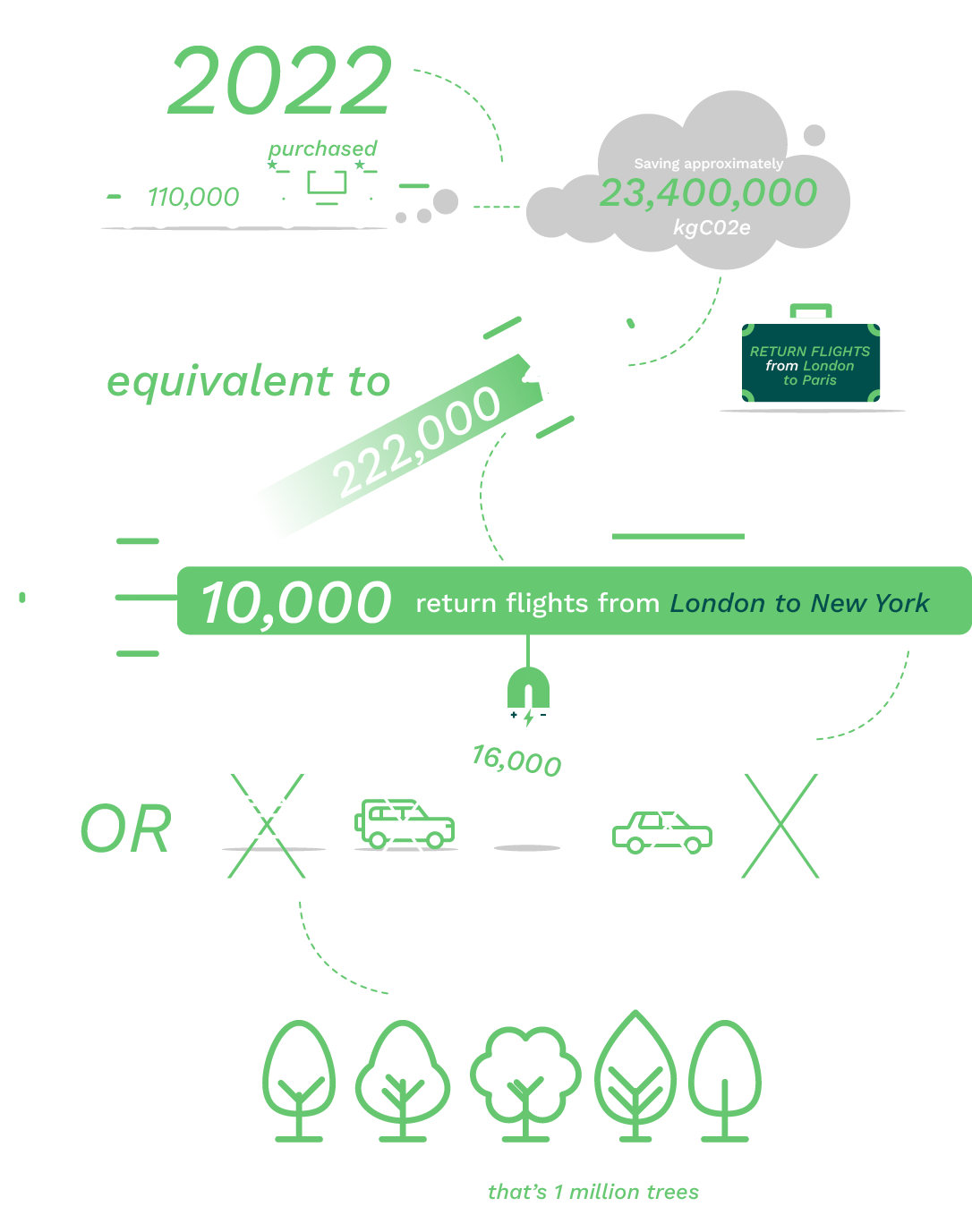
By extending the life-cycle of all devices and creating less electronic waste, we provide our customers with premium grade refurbished tech at a fraction of the new price.
Buying refurbished also decreases the demand for new equipment, which helps to preserve the earth’s ever dwindling, precious resources.
Sustainable consumption and production is about doing more – and better – with less. Decoupling economic growth from environmental degradation, increasing resource efficiency and promoting sustainable lifestyles.
tier1 remains focussed on enhancing our resources, capabilities and compliance in line with the evolving needs of our clients’ and changing legislative requirements.
Our mission is to drive decarbonisation through our sustainable and socially responsible, circular economy business.
By extending the life-cycle of all devices and creating less electronic waste, we provide our customers with premium grade refurbished tech at a fraction of the new price.
Buying refurbished also decreases the demand for new equipment, which helps to preserve the earth’s ever dwindling, precious resources.
Sustainable consumption and production is about doing more – and better – with less. Decoupling economic growth from environmental degradation, increasing resource efficiency and promoting sustainable lifestyles.
When tier1 refurbish devices it is to the highest standard.
All items are fully tested, cleaned, refurbished and quality checked in-house to ensure each product matches our high standards of quality, sustainability and reliablity.
Environmentally Focussed Lifecycle Services
Choosing tier1 as your lifecycle services partner ensures an environmentally focused approach to your requirements – we want to ensure we are all part of the solution and continue to champion a policy of “reuse not recycling, dispersal not destruction”.
UN Sustainable Development Goal 12
We are aligned with the United Nations SDG12 goal “Responsible production and consumption”. Sustainable consumption and production is about doing more – and better – with less. Decoupling economic growth from environmental degradation, increasing resource efficiency and promoting sustainable lifestyles.
 UN Sustainable Development Goal 12
UN Sustainable Development Goal 12
We are aligned with the United Nations SDG12 goal “Responsible production and consumption”. Sustainable consumption and production is about doing more – and better – with less. Decoupling economic growth from environmental degradation, increasing resource efficiency and promoting sustainable lifestyles.
Ecovadis Sustainability Rating
As part of our commitment to society, our people and the environment, tier1 completes a thorough assessment of its business sustainability practices every year through EcoVadis, the global standard for business sustainability ratings. The EcoVadis assessment includes 21 sustainability criteria across four core themes: Environment, Labour & Human Rights, Ethics and Sustainable Procurement. In our latest rating, we earned a Silver medal.
Continuous and effective management of sustainability practices is critical to our business and society. We leverage EcoVadis to rate our performance, identify risks and to understand where we can improve and make a bigger impact across the world. We are committed to continuously monitoring and managing our own performance and that of our partners.
CRN Award Winner 2023
tier1 has achieved a significant milestone by securing the esteemed CRN Channel Award for “Best ESG Project/Initiative”.
Our winning entry showcased the innovative circular approach of tier1, with a particular focus on our impactful Prison Programme. This accolade serves as a profound acknowledgment of the dedication and passion exemplified by our exceptional team. Emerging victorious in a highly competitive category underscores the exceptional diligence and commitment demonstrated by every member of the tier1 team. This award not only recognises our achievements but also underscores the strategic importance of our initiatives in effecting positive change in the world.
E-Waste
One of the key ingredients of tier1’s success is the focus and commitment we place on the environment. tier1 work tirelessly to ensure that we champion a policy of “reuse not recycling, dispersal not destruction”. Our Lifecycle Services ensure the safe, secure, and environmentally friendly disposal of legacy IT Equipment.
Assets received that cannot be resold are stripped for working components and reused where possible. Items that have reached end of life are recycled for circuit boards, power units and separated into different types, ready for refining.
With e-waste estimated to be one of the largest growing waste streams globally, this contributes to reducing excessive consumption of the world’s precious, and ever dwindling, resources – as well as the contribution to climate change, pollution and conflict mining.
tier1 are ISO14001 accredited, meet all EU and UK legislative requirements regarding the recycling of IT equipment including the 1990 Environmental Protection Act and the WEEE Directive. tier1 are a registered Waste Carrier, hold a Waste Management Licence and are an AATF (Approved Authorised Treatment Facility), registered with the Environment Agency.
Zero Landfill
tier1 endeavour to adhere, wherever possible, to a zero landfill policy and ensure we deal with all IT Asset Disposal in the most environmentally friendly way. We promote the reuse of all equipment and work closely with our clients to improve awareness of environmentally favourable options, reducing their own impact on the environment.
Devices which can’t be reused are either recycled at our Maldon site or at our recycling plant at HMP Hindley.
We also work with specific downstream partners for the responsible disposal of specific products that are beyond economical repair and expect all suppliers/vendors to be aware of their own processes and effect it could have on the environment.
We have a strong Environmental Policy, ensuring compliance with all current relevant environmental legislation, including the WEEE directive, and work in partnership with staff and clients to help raise awareness of environmental issues and to make continuing improvements to our operations, always focusing on reducing both our own carbon footprint and that of our clients.
Downstream Partners
tier1’s facility is used for the initial processing of all IT equipment. At our facility, we sort, test, destroy data, clean and – as a priority – resell the items. Items that cannot be resold are stripped for working components. Items that have reached end of life are then stripped of circuit boards, power units and then separated into different types ready for refining. tier1 then utilise our downstream partners for the final refining of items that are now of no practical use. The items are refined for raw materials and used within the supply chain for manufacturing plastic items or refined for different metals. Annually we carry out Duty of Care visits at each of these partners where we inspect the site, processes, insurances, and all other aspects of their business as set out in our duty of care visit questionnaire.
Our Facility
We actively pursue continual improvement in our environmental performance. On an annual basis we audit our supply chain to ensure adherence to our values and the wider environmental framework, for some this involves physical audit of the supplier premises.
Examples of Energy Efficiency Measures include:
- Use of LED low energy lighting where possible and lights on timers and motion sensors
- Use of pool cars which can be maintained and serviced
- Recycling of all office waste
- Reduced water usage, using filtered water machines and low energy water heaters which are serviced regularly
- Duplex black and white printing managed for all users by default
- Air emissions from our fleet are reduced through the daily driver checks ensuring tyre pressures are maintained, tyre tread is maintained, issues are reported and fixed within acceptable timescales
- The tier1 fleet is also serviced every 12 weeks as per regulations
- Increasing the use of teleconference software (Skype for Business and Microsoft Teams) to reduce business travel
- Power down of IT systems over weekends to reduce energy consumption
- All plant within tier1 is subject to an annual maintenance plan which sets out the schedule of maintenance (daily, weekly, monthly, quarterly, 6 monthly, annually), scope of maintenance (visual inspection, full inspection, 3rd party contracted maintenance) issue escalation, fault fixing report log
- Use of water-based cleaning products that are labelled zero VOC
- The tier1 Quality Team monitor monthly ensuring the schedule is maintained

Reduce. Reuse. Redeploy. Recycle
Circular Approach to Sustainability
We ensure that the Lifecycle Services we provide are sustainable and circular in approach, and actively promote the reuse of all equipment where possible. We work closely with our clients to improve awareness of environmentally favourable solutions, ensuring recycling is the last option considered and making a real contribution to your ESG goals.
Reduce. Reuse. Redeploy. Recycle
Circular Approach to Sustainability

We ensure that the Lifecycle Services we provide are sustainable and circular in approach, and actively promote the reuse of all equipment where possible. We work closely with our clients to improve awareness of environmentally favourable solutions, ensuring recycling is the last option considered and making a real contribution to your ESG goals.